How It Works
Paste a link. Get an answer. Here's what happens and how to read it.
Using url.vet
- 1
Paste any link
Drop a URL into the input box — full link, shortened link, or just a domain like example.com. url.vet will normalize it.
- 2
Hit Check
The scan runs live. It takes a few seconds because url.vet actually fetches the page rather than looking it up in a static database.
- 3
Read the result
You'll get a trust score from 0 to 100, a verdict, and a breakdown of every signal that contributed to it.
Reading the Result
The trust score
A number from 0 to 100. Higher is safer. 50 is the neutral baseline — a brand new unknown URL with no signals in either direction. Most legitimate sites score above 65; anything below 30 has serious red flags.
Risky
score below 30
Suspicious
score 30 to 64
Safe
score 65 and above
The signal breakdown
Below the score you'll see every check that ran, grouped into sections: URL structure, DNS, TLS, domain intelligence, content, and threat feeds. Each one shows a green checkmark, a red flag, or a neutral note. Red flags increase the risk score; green checkmarks build trust. Neutral notes are shown for context but don't affect the score.
The page preview
url.vet takes a live screenshot of the page. It's one of the fastest ways to spot a phishing site — if the page looks like your bank's login screen but the domain has nothing to do with your bank, that's a red flag no automated check can fully capture.
Sharing a result
Every scan has a permanent shareable URL. Use it to send a result to a colleague, post it in a security thread, or report a suspicious link to someone who needs context. The link includes the verdict and score so recipients see the summary without having to re-scan.
Under the Hood
18 checks run concurrently the moment you submit. Each one is independent — a timeout or failure in one never delays the others.
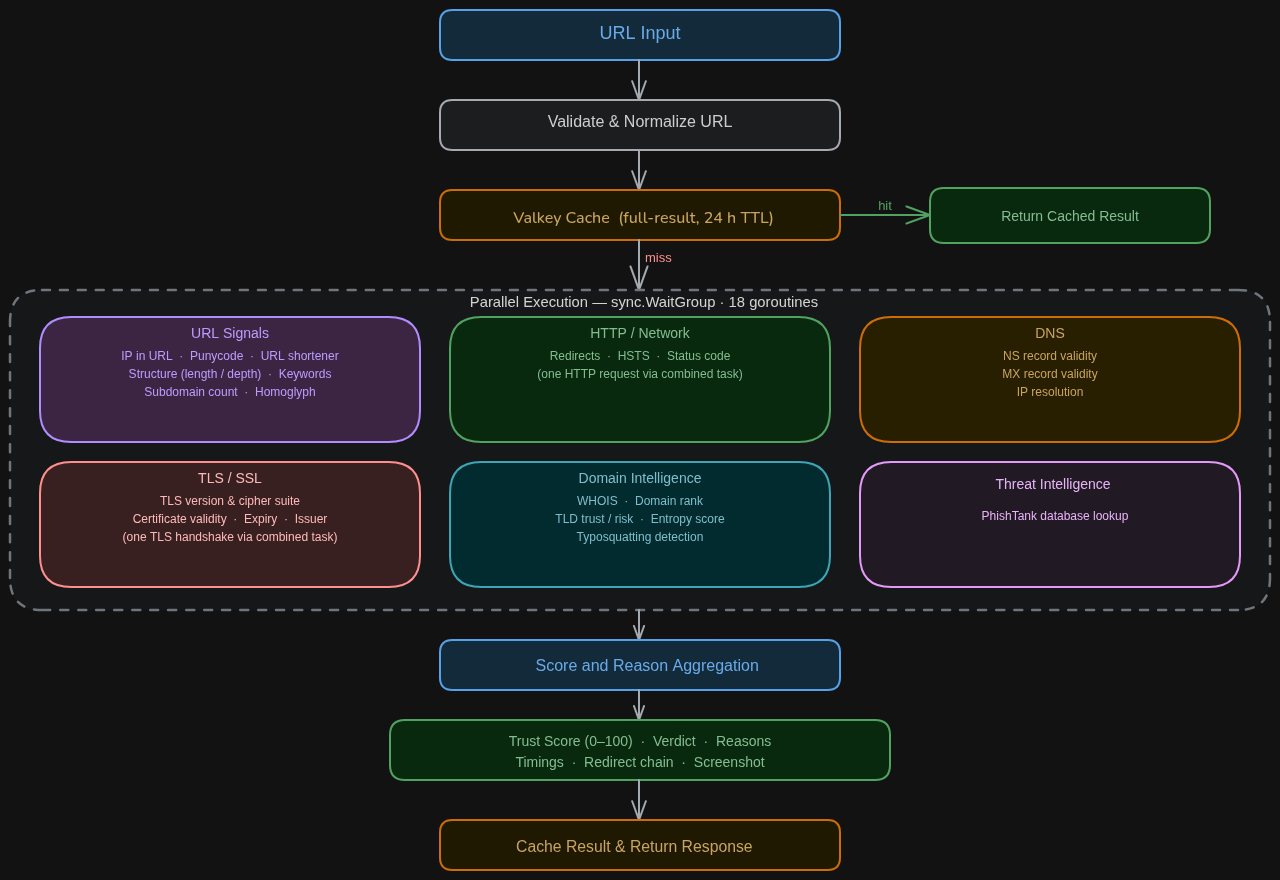
URL structure
Inspects the link itself before any network request: IP-as-hostname, URL shorteners, suspicious path keywords, IDN homograph encoding, subdomain depth.
HTTP / Network
Makes one real request and follows every redirect. Checks HSTS, status code, and whether the final destination is a different domain than what you clicked.
DNS
Verifies NS and MX records exist and that the domain resolves to a real IP.
TLS / SSL
Checks certificate validity, expiry, issuer, Certificate Transparency log inclusion, and known-bad fingerprints.
Domain intelligence
Looks up domain age via WHOIS, global traffic rank, TLD classification, DNSSEC, Shannon entropy, and typosquatting against 500+ brands.
Content analysis
Fetches and parses the page. Detects login and payment forms on suspicious domains, hidden iframes, brand impersonation, and forms that exfiltrate data to third parties.
Threat intelligence
Cross-references against PhishTank's confirmed and reported phishing databases.
Limitations
Heuristic detection means false positives are possible. A legitimate site that's new and unranked might score lower than it deserves. No tool is a guarantee.
There's no ML model, and that's intentional. A model that can't explain itself isn't useful when you need to make a trust decision in the moment. Every signal here can be read and reasoned about.
Use url.vet as one layer of defense, not the only one.
Got a link you're not sure about?
Check it on url.vet